Access Server subscriptions are based on the needed number of simultaneous VPN connections. While others charge based on the number of CPU cores or the bandwidth of the server, OpenVPN does not. Start the OpenVPN server, send the client configuration and certificate files to the clients, and start OpenVPN connect on the client side. The client now should be connected to the OpenVPN server, have access to internet and have access to LAN resources at the server side. (2021/01/19 edit) Also make sure you don't enable IPv6 on your router.
- Openvpn Access Server License Key Generator
- Openvpn Access Server License Key Generator
- Openvpn Access Server License Key Free
- Openvpn Access Server License Key Free
OpenVPN is a commercial VPN solutions service to secure your data communications. You can use this in number of ways like hiding your internet identity, remote access to company, inside IoT security and many more. My most favorite use of OpenVPN is to use it as SSH whitelisting, so you can SSH to your server instances only when you are connected to a certain VPN.
Remember, OpenVPN service is not free, but it's cost is very affordable and reasonable for a personal as well as corporate setup!
Overview of AWS setup :
When you spin up an EC2 instance on AWS, you can either choose from vanilla instance AMIs like basic centos or ubuntu 16.x etc. OR you can choose from pre-baked marketplace AMIs. Services like OpenVPN use marketplace AMIs to provide their pre-baked instances which are ready to use.
But wait.. It is not that plug and play. Setting up OpenVPN can be tricky specially when you do not know the sequence of steps and some little tricks. But, we have got you covered.
We will be also dealing with the common problem of untrusted SSL certificate error and install a free CertBot SSL to make your OpenVPN server full proof. Let's get started!
Step 1 - Spinning up the EC2 server :
- Login to your AWS Console and go to the region you want yout OpenVPN instance to be in
- Select EC2 service and click on
Launchto spin up a new instance - The EC2 launch wizard will be shown, where click on
AWS Marketplaceon left - Now search for
openvpnand pressenter - It will show number of official OpenVPN marketplace AMIs which are different in the number of connected devices. I will strongly recommend if you are doing it for the first time, choose the first one which will give you 2 concurrent devices to start with. You can anytime purchase a new license for extending number of users.
- Now click on
selectwhen you have choosen your AMI - You will be prompted with OpenVPN service cost for each instance type you spin up. This will be added to your AWS billing. I would always choose
t2.microinstance type as OpenVPN server does not need much memory to perform it's operations.
- Click on
continueand choose instance type ast2.micro - Click on
Next: Configure Instance Details - This is an important step. Make sure you choose your VPC if you have one and choose it's public subnet. If you do not have custom VPC and subnets, leave these settings as is. Make sure that its a public subnet as OpenVPN instance should be in a public subnet so it is accessible via web directly.
- Click on
Next: Add Storage - Here you need to make sure the instance volume is encrypted. Otherwise you will get warning like
Volume (/dev/sda1) needs to be encrypted as encryption is enabled by default.Click onEncryptiondropdown and choose a KMS key which will encrypt your volume. Also make sure your instance volume type isGeneral Purpoise SSD (gp2). Sometimes it changes toMagnetic (standard)when you enable volume encryption - Click on
Next: Add Tagsand add the tags you need for this instance - Click on
Next: Configure Security Group - You need to select
Create a new security group. Add security group name asOpenVPN server SG. Wait.. Hey, AWS already has filled in the group rules for you, thats awesome... isn't it?
- Click on
Review and Launch - Verify the details once in this final summary screen and click on
Launch - It will ask you to select a
key paircreate a new one asOpenVPN-key-pairand download it. - Now finally.. Click on
Launch Instances
You are done with launching the instance.. Yassssss!! Above steps will launch your new server.
Step 2 - Assigning elastic IP and domain :
When your instance is up and running, you will see it's public IP given by AWS automatically. However, once you reboot this instance anytime, this IP will change. We do not want that. So we will associate an elastic IP to this instance so it stays no matter if the instance is stopped or rebooted.
- Select EC2 service from the same region where you have the OpenVPN instance
- Click on
Elastic IPs - Click on
Allocate new addressand selectAllocate - Now you will see a new elasic IP in the list which is not associated with any instance
- Select that IP and in the actions dropdown choose
Associate Address - You will see a new association form, keep resource type as
Instanceand select your new OpenVPN instance from the instance dropdown - Save the association
- Now of you go back to the instance and see it's public IP, you will see the new elastic IP as its public IP.
Now, you can associate a domain to this new public IP or you can keep as it is. It depends on your preference but I would recommend having a domain like vpn.yourdomain.com to access this server.
If you choose to have a domain, then this is the time when you need to point the A record of your domain to the new elastic public IP. For the consistency in remaining article, we are going to use vpn.yourdomain.com.
Step 3 : Initializing up the OpenVPN basic settings :
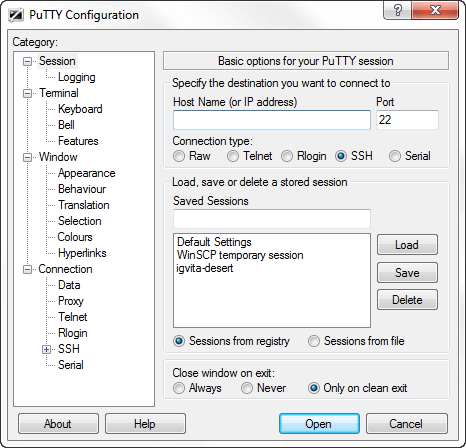
Now, you will not be able to access openVPN directly. This is because you are yet to initiate the basic settings. For that, we need to ssh into the server.
- Use the key pair file
OpenVPN-key-pair.pemto ssh into the instance. As in the security group port22is open for everyone with value0.0.0.0/0, you would be able to SSH to your instance from anywhere. (We will change that after the setup is completed) - Use ssh username as
openvpnasas this comes default with the OpenVPN marketplace AMI - Once you login to the instance, you will see a setup wizard and it will ask you to agree to the terms and conditions
- Now it will ask number of settings to you :
- Now you we need a password to login first time as an admin. For that run command
You are done with basic setup, we can now proceed with the web UI for further settings.
Step 4 : Accessing OpenVPN Web UI :
Now we will access the OpenVPN Web UI using the elastic IP with url https://x.x.x.x:943/admin where x.x.x.x is your elasic IP. You might be thinking that we have vpn.yourdomain.com setup so why are we using the elastic IP? We will get back to it shortly but for the first time we will need to use the IP.
- Visit https://x.x.x.x:943/admin which will say that it is insecure, click on advanced and proceed to visit the website
- Login with the username
openvpnand the admin password you set earlier - Once you login for the first time, you will see a lisence agreement which you select
agree
- Now you will see a nice web UI as below :
- Go to
Configuration > Network Settingson the left hand side menu - You will see a setting
Hostname or IP Address. Here we will now entervpn.yourdomain.com - Now click on
Save Settings - Now click on
Update running server
Now we have the domain set up. You can open another tab and visit https://vpn.yourdomain.com:943/admin and it will work now!
Step 5 : Having a valid SSL :
You must have observed that the SSL comes with the OpenVPN server is not trusted by browsers. So we will have a new CertBot SSL which will not show SSL warnings and errors.
- SSH to the openvpn server again
- Type following commands to install certbot
Now we need to open port 80 temporarily on the security group of our OpenVPN server so that Certbot can verify that the server and domain. Certbot will temporarily spin up a webserver on our openVPN machine for the same.- Go to AWS console and choose our OpenVPN server security group OpenVPN server SG- In the inbound rules, add HTTP 80 rule with source 0.0.0.0/0, ::/0 to access tempoarary port 80 traffic
Now we can run Certbot
- SSH to the openvpn server again
- Type following commands to request certbot certificate
It will ask you number of questions and then a domain name. Enter vpn.yourdomain.com and it will verify it using temporary web server on port 80.
Below is the output :
Now we are concerned with 2 files : privkey.pem and fullchain.pem. But first, go back to the security group and remove the rule for HTTP port 80 as we do not need it anymore!
Now we will view contents of these files and copy them locally. You can use following commands to show their text content, you need to manually copy them and make new files locally with same name and paste the respective contents.
Final step is to update these certificates on OpenVPN web UI. - Visit https://vpn.yourdomain.com:943/admin and login with the admin credentials used earlier- Go to Configuration > Web Server on the left hand side menu- You will 3 file upload options fot uploading certifiates- Upload local fullchain.pem for Certificate file upload- Upload local privkey.pem for Private Key file upload- Click on Validate and you will see new certificate results under Validation Results- Now click on Save- Click on Update running server if it pops up
And now you are done! Logout and login again or a new tab and you will see that new SSL works with no certificate warnings.
Step 6 : Creating an OpenVPN user :
You should never ever use the admin user openvpn to connect via vpn client! We will now create a new user.
- Visit
https://vpn.yourdomain.com:943/adminand login with the admin credentials used earlier - Go to
User Management > User Permissionson the left hand side menu - Enter new username
vpnclientuserand click onMore SettingsDropdown to set a new passsword - Click on
Save SettingsandUpdate existing server
Final step : Login with VPN :
Go to your VPN client and enter host as vpn.yourdomain.com with username as vpnclientuser and the password you set for it. And Done!! You are connected.
If you do not have VPN client follow below steps :
- Visit
https://vpn.yourdomain.com:943(Note that this url is not the admin login but a user login without /admin at the end) - Login with the user credentials with username as
vpnclientuserand the password you set for it - Now you will see options to download VPN client or reset the user password if needed
Cleanup :
Now you are done with the OpenVPN server setup. I would recommend to remove the HTTP 22 inbound rule from OpenVPN server SG security group associated with the VPN server. This is because you would only need SSH access when you want to check logs or update some setup on OpenVPN. You can always go to AWS and open the port when needed.
Alternatively, change the source to your specific IP from which you SSH to the instance so that it is not open to the whole wide internet.
In this HOWTO, I have demostrated how to deploy a OpenVPN server on AWS, and how to connect your AWS resources from end user devices through OpenVPN client program.
What is OpenVPN Server ?
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for key exchange.
AWS provides this OpenVPN server as an AMI to provide secured point-to-point connection between your AWS site to your site situated anywhere in the world. This will be helpful for mobile users want to connect your company AWS resources in a secure way.
So, this HOWTO explains how to setup a Software Defined Private Network in AWS cloud environment, and how a client can connect his AWS resources through OpenVPN server.
8 Steps total
Step 1: Preparing your Environment
What are all the components involved in this preparation -
OpenVPN Access Server Appliance [In the form of : AMI]
OpenVPN Client Software
VPC Configuration hosted at AWS
Licensing :
OpenVPN Access Server licensing comes pre-bundled with your Amazon EC2 instance providing the flexibility of hourly billing with no upfront costs or long-term investments i.e in one word : Pay As You Go.
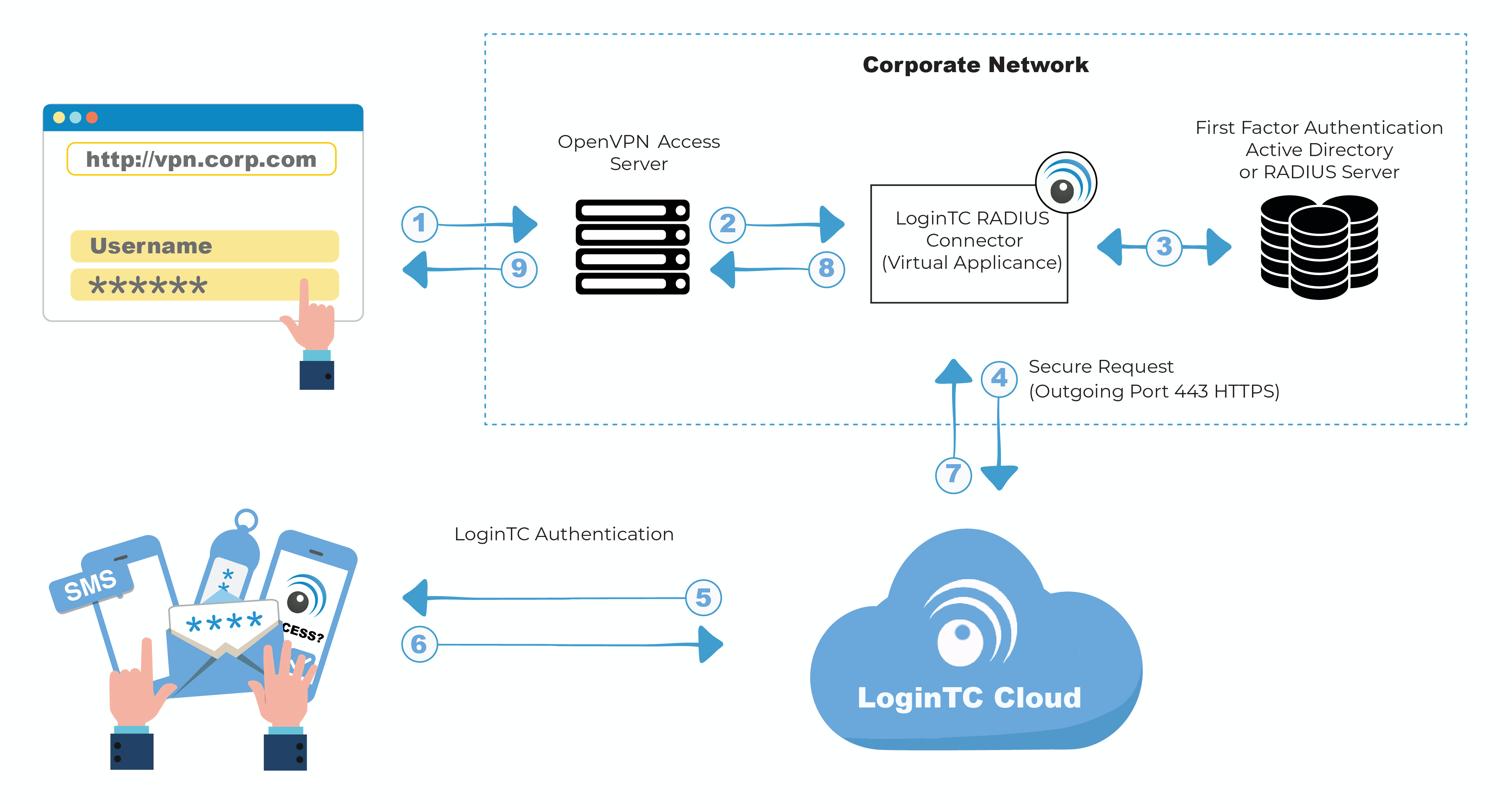
Let's assume that you already have a basic hands-on experience in AWS cloud services like hosting VPC and launching instances. Below diagram shows clearly how a remote user connected to AWS private network using Open VPN Gateway client through a secured VPN tunnel.
Step 2: Launching Open VPN Server Appliance
On our first step, we are launching Open VPN Server Appliance from AWS Market place. Note that, Open VPN Server instance will be charged as per the no of concurrent connection license it has. You can choose any Open VPN server appliance as per your need.
First login to AWS Market Place with a valid AWS console login.
https://aws.amazon.com/marketplace/
Enter OpenVPN Access Server in the search window, and press Enter.
Step 3: Launching Open VPN Server Appliance - Step 2
Search result will shows available Open VPN Server instances with various connection count. Please note that, depends on connection count and Region of deployment your monthly bill will vary.
Select any one of the Open VPN Server appliance for deployment.
Step 4: Launching Open VPN Server Appliance - Step 3
Click continue to launch the instance. For a simple launch process, choose '1-Click Launch' option and proceed with default option, However user can always have flexibility to make fine adjustments like Changing AWS 'Region',EC2 Instance Type, VPC Settings and security group information.
While launching the Server Appliance, you will be noted to create a new key pair to connect the instance. Create a new pair and keep it safely to connect the instance later.
Openvpn Access Server License Key Generator
Click 'Launch with 1 click' button after you have confirmed all of the selected options are correct.
To confirm that the instance has successfully launched, watch the Instances section for status. You should see something similar to the following as your instance is being launched. Once you see 'Instant status' is running, your Open VPN Server Appliance is ready for configuration.
Step 5: Assigning an Elastic IP to the Instance
Though its option, you should allocate a static IP address for your appliance so the IP address can be reclaimed in case of AWS machine failure/shutdown/reboot. To do so, visit the Elastic IPs section in the left navigation panel.
Step 6: Configuring OpenVPN Access Server Instance
Once your new instance is successfully launched and running, you will need to SSH into the console using a SSH client software and the private key pair you have used/created previously.
When login screen is prompted, use openvpnas as the username, and then press Enter. (NOTE: If you are using previous versions of our appliance, the username used is root instead of openvpnas)
If the private key you have specified was correct, you should now be logged in and the OpenVPN Access Server Setup Wizard should now be started. Follow the instructions below to begin configuring your server.
Read through the EULA, and enter yes to indicate your agreement acceptance.
>> Will this be the primary Access Server node?
Default: Yes, Press Enter to accept the default setting. Otherwise, if you are setting up your failover node, change this to say no. Here we are setting up primary Access Server node. So default selected.
>> Please specify the network interface and IP address to be used by the Admin Web UI:
Default : 2, Choose 1 – 'all interfaces: 0.0.0.0' to listen in all interface.
>> Please specify the port number for the Admin Web UI.
Default: 943, It is usually safe to leave this at the default port unless customization is desired.
>> Please specify the TCP port number for the OpenVPN Daemon
Default: 443, It is usually safe to leave this at the default port unless customization is desired.
>> Should client traffic be routed by default through the VPN?
Default: No, If you only have a small network you would like your remote users to connect over the VPN, select no. Otherwise, if you would like everything to go through the VPN while the user is connected (especially useful if you want to secure data communications over an insecure link), select yes for this option.
>> Should client DNS traffic be routed by default through the VPN?
Default: no, If you would like your VPN clients to able to resolve local domain names using an on-site DNS server, select yes for this option. Otherwise, select no. Do note that if you selected yes for the previous option, all traffic will be routed over the VPN regardless what you set for this setting here.
>> Use local authentication via internal DB?
Default: yes, If you would like OpenVPN Access Server to keep an internal authentication database for authenticating your users, select yes for this option. When this option is turned on, you will be able to define and/or change username and passwords within the Admin Web UI.
>> Should private subnets be accessible to clients by default?
Default: yes, This option defines the default security setting of your OpenVPN Access Server. When Should client traffic be routed by default through the VPN.
>> Do you wish to login to the Admin UI as 'openvpn'?
Default: Yes, This defines the initial username in which you would use to login to the Access Server Admin UI area. This username will also serve as your 'lock out' administrator username shall you ever lock yourself out of your own server. If you would like to specify your own username, select no. Otherwise, accept yes for the default.
> > Please specify your OpenVPN-AS license key (or leave blank to specify later):
Explanation: If you have purchased a license key for your OpenVPN Access Server software, enter it here. Otherwise, leave it blank. OpenVPN Access Server includes two free licenses for testing purpose.
>> Create password for the OpenVPN admin user, invoking the below command.
sudo passwd openvpn
Enter new UNIX password:
Retype new UNIX password:
Last thing we need to do before we can connect to the admin area and to our VPN is disable the Source/Destination check in AWS. Without doing this we would not be able to access our private subnets.
To change this go to the EC2 console in AWS, select your instance, choose *Actions>Networking>Change Source/Dest. Check* as seen below. Choose 'Yes, Disable' on the next screen.
Step 7: Testing OpenVPN server connectivity
Here, we are setting up a test instance on the same private subnet VPC where the OpenVPN server exist.
Openvpn Access Server License Key Generator
1.Login to your AWS account and navigate to the EC2 Dashboard and click 'Launch Instance' on the left.
Press 'Select' next to the top item *Amazon Linux AMI*
2. Leave on t2.micro and click 'Next: Configure Instance Details.'
3. Make sure to set your subnet into your private subnet mentioned in the prerequisites. Then click 'Review and Launch' as defaults for everything else are fine for this test.
Step 8: Connecting AWS instance from the client

Install the OpenVPN client on end user machine and connect to the instance running in the private subnet on AWS.
In your web browser enter the Elastic IP from your OpenVPN Access Server https://elastic-ip-here:943 Note: On your first attempt to connect you will be warned by your browser that the SSL certificate cannot be validated. This is OK for our demo but in a real world you will want to setup a real SSL certificate in your setup.
On the screen enter 'openvpn' for the Username and the password you created for the user.
After your credentials are accepted you will see the screen below. Go ahead and click 'Click here to continue' which will download the OpenVPN client installer to your machine.
Thus, Open VPN Server appliance is deployed on our AWS account, and you can create as many AMIs on that created VPC. Now authenticated users can login to connect their AWS AMIs securely through the installed VPN Client.
Deploying a Open VPN server providing an extra security for the end users, and it is easy to deploy a OpenVPN server on your AWS account.
- Login with the username
openvpnand the admin password you set earlier - Once you login for the first time, you will see a lisence agreement which you select
agree
- Now you will see a nice web UI as below :
- Go to
Configuration > Network Settingson the left hand side menu - You will see a setting
Hostname or IP Address. Here we will now entervpn.yourdomain.com - Now click on
Save Settings - Now click on
Update running server
Now we have the domain set up. You can open another tab and visit https://vpn.yourdomain.com:943/admin and it will work now!
Step 5 : Having a valid SSL :
You must have observed that the SSL comes with the OpenVPN server is not trusted by browsers. So we will have a new CertBot SSL which will not show SSL warnings and errors.
- SSH to the openvpn server again
- Type following commands to install certbot
Now we need to open port 80 temporarily on the security group of our OpenVPN server so that Certbot can verify that the server and domain. Certbot will temporarily spin up a webserver on our openVPN machine for the same.- Go to AWS console and choose our OpenVPN server security group OpenVPN server SG- In the inbound rules, add HTTP 80 rule with source 0.0.0.0/0, ::/0 to access tempoarary port 80 traffic
Now we can run Certbot
- SSH to the openvpn server again
- Type following commands to request certbot certificate
It will ask you number of questions and then a domain name. Enter vpn.yourdomain.com and it will verify it using temporary web server on port 80.
Below is the output :
Now we are concerned with 2 files : privkey.pem and fullchain.pem. But first, go back to the security group and remove the rule for HTTP port 80 as we do not need it anymore!
Now we will view contents of these files and copy them locally. You can use following commands to show their text content, you need to manually copy them and make new files locally with same name and paste the respective contents.
Final step is to update these certificates on OpenVPN web UI. - Visit https://vpn.yourdomain.com:943/admin and login with the admin credentials used earlier- Go to Configuration > Web Server on the left hand side menu- You will 3 file upload options fot uploading certifiates- Upload local fullchain.pem for Certificate file upload- Upload local privkey.pem for Private Key file upload- Click on Validate and you will see new certificate results under Validation Results- Now click on Save- Click on Update running server if it pops up
And now you are done! Logout and login again or a new tab and you will see that new SSL works with no certificate warnings.
Step 6 : Creating an OpenVPN user :
You should never ever use the admin user openvpn to connect via vpn client! We will now create a new user.
- Visit
https://vpn.yourdomain.com:943/adminand login with the admin credentials used earlier - Go to
User Management > User Permissionson the left hand side menu - Enter new username
vpnclientuserand click onMore SettingsDropdown to set a new passsword - Click on
Save SettingsandUpdate existing server
Final step : Login with VPN :
Go to your VPN client and enter host as vpn.yourdomain.com with username as vpnclientuser and the password you set for it. And Done!! You are connected.
If you do not have VPN client follow below steps :
- Visit
https://vpn.yourdomain.com:943(Note that this url is not the admin login but a user login without /admin at the end) - Login with the user credentials with username as
vpnclientuserand the password you set for it - Now you will see options to download VPN client or reset the user password if needed
Cleanup :
Now you are done with the OpenVPN server setup. I would recommend to remove the HTTP 22 inbound rule from OpenVPN server SG security group associated with the VPN server. This is because you would only need SSH access when you want to check logs or update some setup on OpenVPN. You can always go to AWS and open the port when needed.
Alternatively, change the source to your specific IP from which you SSH to the instance so that it is not open to the whole wide internet.
In this HOWTO, I have demostrated how to deploy a OpenVPN server on AWS, and how to connect your AWS resources from end user devices through OpenVPN client program.
What is OpenVPN Server ?
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for key exchange.
AWS provides this OpenVPN server as an AMI to provide secured point-to-point connection between your AWS site to your site situated anywhere in the world. This will be helpful for mobile users want to connect your company AWS resources in a secure way.
So, this HOWTO explains how to setup a Software Defined Private Network in AWS cloud environment, and how a client can connect his AWS resources through OpenVPN server.
8 Steps total
Step 1: Preparing your Environment
What are all the components involved in this preparation -
OpenVPN Access Server Appliance [In the form of : AMI]
OpenVPN Client Software
VPC Configuration hosted at AWS
Licensing :
OpenVPN Access Server licensing comes pre-bundled with your Amazon EC2 instance providing the flexibility of hourly billing with no upfront costs or long-term investments i.e in one word : Pay As You Go.
Let's assume that you already have a basic hands-on experience in AWS cloud services like hosting VPC and launching instances. Below diagram shows clearly how a remote user connected to AWS private network using Open VPN Gateway client through a secured VPN tunnel.
Step 2: Launching Open VPN Server Appliance
On our first step, we are launching Open VPN Server Appliance from AWS Market place. Note that, Open VPN Server instance will be charged as per the no of concurrent connection license it has. You can choose any Open VPN server appliance as per your need.
First login to AWS Market Place with a valid AWS console login.
https://aws.amazon.com/marketplace/
Enter OpenVPN Access Server in the search window, and press Enter.
Step 3: Launching Open VPN Server Appliance - Step 2
Search result will shows available Open VPN Server instances with various connection count. Please note that, depends on connection count and Region of deployment your monthly bill will vary.
Select any one of the Open VPN Server appliance for deployment.
Step 4: Launching Open VPN Server Appliance - Step 3
Click continue to launch the instance. For a simple launch process, choose '1-Click Launch' option and proceed with default option, However user can always have flexibility to make fine adjustments like Changing AWS 'Region',EC2 Instance Type, VPC Settings and security group information.
While launching the Server Appliance, you will be noted to create a new key pair to connect the instance. Create a new pair and keep it safely to connect the instance later.
Openvpn Access Server License Key Generator
Click 'Launch with 1 click' button after you have confirmed all of the selected options are correct.
To confirm that the instance has successfully launched, watch the Instances section for status. You should see something similar to the following as your instance is being launched. Once you see 'Instant status' is running, your Open VPN Server Appliance is ready for configuration.
Step 5: Assigning an Elastic IP to the Instance
Though its option, you should allocate a static IP address for your appliance so the IP address can be reclaimed in case of AWS machine failure/shutdown/reboot. To do so, visit the Elastic IPs section in the left navigation panel.
Step 6: Configuring OpenVPN Access Server Instance
Once your new instance is successfully launched and running, you will need to SSH into the console using a SSH client software and the private key pair you have used/created previously.
When login screen is prompted, use openvpnas as the username, and then press Enter. (NOTE: If you are using previous versions of our appliance, the username used is root instead of openvpnas)
If the private key you have specified was correct, you should now be logged in and the OpenVPN Access Server Setup Wizard should now be started. Follow the instructions below to begin configuring your server.
Read through the EULA, and enter yes to indicate your agreement acceptance.
>> Will this be the primary Access Server node?
Default: Yes, Press Enter to accept the default setting. Otherwise, if you are setting up your failover node, change this to say no. Here we are setting up primary Access Server node. So default selected.
>> Please specify the network interface and IP address to be used by the Admin Web UI:
Default : 2, Choose 1 – 'all interfaces: 0.0.0.0' to listen in all interface.
>> Please specify the port number for the Admin Web UI.
Default: 943, It is usually safe to leave this at the default port unless customization is desired.
>> Please specify the TCP port number for the OpenVPN Daemon
Default: 443, It is usually safe to leave this at the default port unless customization is desired.
>> Should client traffic be routed by default through the VPN?
Default: No, If you only have a small network you would like your remote users to connect over the VPN, select no. Otherwise, if you would like everything to go through the VPN while the user is connected (especially useful if you want to secure data communications over an insecure link), select yes for this option.
>> Should client DNS traffic be routed by default through the VPN?
Default: no, If you would like your VPN clients to able to resolve local domain names using an on-site DNS server, select yes for this option. Otherwise, select no. Do note that if you selected yes for the previous option, all traffic will be routed over the VPN regardless what you set for this setting here.
>> Use local authentication via internal DB?
Default: yes, If you would like OpenVPN Access Server to keep an internal authentication database for authenticating your users, select yes for this option. When this option is turned on, you will be able to define and/or change username and passwords within the Admin Web UI.
>> Should private subnets be accessible to clients by default?
Default: yes, This option defines the default security setting of your OpenVPN Access Server. When Should client traffic be routed by default through the VPN.
>> Do you wish to login to the Admin UI as 'openvpn'?
Default: Yes, This defines the initial username in which you would use to login to the Access Server Admin UI area. This username will also serve as your 'lock out' administrator username shall you ever lock yourself out of your own server. If you would like to specify your own username, select no. Otherwise, accept yes for the default.
> > Please specify your OpenVPN-AS license key (or leave blank to specify later):
Explanation: If you have purchased a license key for your OpenVPN Access Server software, enter it here. Otherwise, leave it blank. OpenVPN Access Server includes two free licenses for testing purpose.
>> Create password for the OpenVPN admin user, invoking the below command.
sudo passwd openvpn
Enter new UNIX password:
Retype new UNIX password:
Last thing we need to do before we can connect to the admin area and to our VPN is disable the Source/Destination check in AWS. Without doing this we would not be able to access our private subnets.
To change this go to the EC2 console in AWS, select your instance, choose *Actions>Networking>Change Source/Dest. Check* as seen below. Choose 'Yes, Disable' on the next screen.
Step 7: Testing OpenVPN server connectivity
Here, we are setting up a test instance on the same private subnet VPC where the OpenVPN server exist.
Openvpn Access Server License Key Generator
1.Login to your AWS account and navigate to the EC2 Dashboard and click 'Launch Instance' on the left.
Press 'Select' next to the top item *Amazon Linux AMI*
2. Leave on t2.micro and click 'Next: Configure Instance Details.'
3. Make sure to set your subnet into your private subnet mentioned in the prerequisites. Then click 'Review and Launch' as defaults for everything else are fine for this test.
Step 8: Connecting AWS instance from the client
Install the OpenVPN client on end user machine and connect to the instance running in the private subnet on AWS.
In your web browser enter the Elastic IP from your OpenVPN Access Server https://elastic-ip-here:943 Note: On your first attempt to connect you will be warned by your browser that the SSL certificate cannot be validated. This is OK for our demo but in a real world you will want to setup a real SSL certificate in your setup.
On the screen enter 'openvpn' for the Username and the password you created for the user.
After your credentials are accepted you will see the screen below. Go ahead and click 'Click here to continue' which will download the OpenVPN client installer to your machine.
Thus, Open VPN Server appliance is deployed on our AWS account, and you can create as many AMIs on that created VPC. Now authenticated users can login to connect their AWS AMIs securely through the installed VPN Client.
Deploying a Open VPN server providing an extra security for the end users, and it is easy to deploy a OpenVPN server on your AWS account.
References
- Vembu Blog
Openvpn Access Server License Key Free
4 Comments
Openvpn Access Server License Key Free
- AnaheimWRXDriver414 Jun 22, 2017 at 06:52pm
Any steps to setup LDAP auth in a windows domain environment by chance?
- Pimientoselvarajmanoharan Jul 24, 2017 at 02:49pm
Hi,
Can you please clear about your question ? You want to know LDAP auth for functionality in windows? or AWS auth with LDAP Protocol ? - Anaheimreeceline Feb 6, 2018 at 08:05pm
Great guide, easy to follow was able to setup OpenVPN.
- Pimientomhghg-2020 Apr 25, 2020 at 06:57am
Can you show us how to set up openvpn server on ubuntu Server 20.04 LTS if possible please?
